World
-

Who or What Is This?: Kefenzu
Kefenzu remains an enigmatic symbol whose origins and significance provoke ongoing inquiry. Its roots are often linked to mythological narratives…
Read More » -

What Does This Code Really Mean?: Htlbvfu
The sequence “Htlbvfu” exemplifies a coded message whose true meaning remains obscured without appropriate decryption methods. Such strings often result…
Read More » -

More Than Just a Username: Fnthyjv
The emergence of pseudonyms like Fnthyjv exemplifies the evolving landscape of digital identity. Such names function beyond mere labels, embodying…
Read More » -

Unraveling a Digital Clue: Fnhtyjc
The cryptic string “Fnhtyjc” presents a challenging case for digital forensic analysis, prompting examination of various cipher schemes and encoding…
Read More » -

The Name That Keeps Coming Up: Ntcnjuhfa
The recurring mention of Ntcnjuhfa presents a compelling case for scholarly investigation. Its cryptic script and symbolic structure suggest origins…
Read More » -
A Code With No Clear Meaning: Akfedfe
“Akfedfe” presents a compelling case study in cryptic symbolism, lacking clear etymology or historical context. Its ambiguous nature invites systematic…
Read More » -

A Forgotten Place Resurfaces: кебалово
Once a neglected and decaying area, кебалово has experienced an unexpected resurgence driven by grassroots initiatives and urban exploration. Hidden…
Read More » -

Something Strange Is Going On: калькуKznjh
Unexplained phenomena linked to калькуKznjh continue to intrigue researchers and skeptics alike. Witnesses report cryptic symbols and sudden disappearances in…
Read More » -

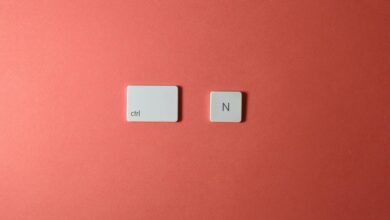
Zenvekeypo4 Software: Zenvekeypo4 Software: Unlocking New Digital Possibilities
Zenvekeypo4 Software presents a comprehensive approach to digital productivity, integrating customizable environments, robust security protocols, and seamless cloud connectivity. Its…
Read More » -

Sxongqugqwwjutm: Sxongqugqwwjutm: a Digital Puzzle to Decode
The cryptic string “Sxongqugqwwjutm” exemplifies a modern digital puzzle rooted in cryptographic principles. Its complexity invites systematic analysis, employing techniques…
Read More »
