Digital Identity Verification Report – phatassnicole23, Pegahmil Venambez, Can Qikatalahez Lift, Zhuzdizos, Herzalladich Lagicallioth, Shopify Wisestudyspot .Com, J 96-085v3z, Nambemil Vezkegah, Wilbertemhof Marijneverpoort, Woziutomaz
The Digital Identity Verification Report synthesizes best practices for onboarding, high-stakes transactions, and ongoing risk management. It emphasizes data minimization, auditable decisions, and risk-based metrics to balance security with usability. The analysis highlights transparent data flows and user empowerment, paired with policy-aligned mitigations to deter fraud. The framework invites scrutiny of modular testing and governance, inviting further examination of how these components cohere in real-world deployments. A critical question remains: how will these principles scale across diverse platforms?
What Digital Identity Verification Is and Why It Matters Today
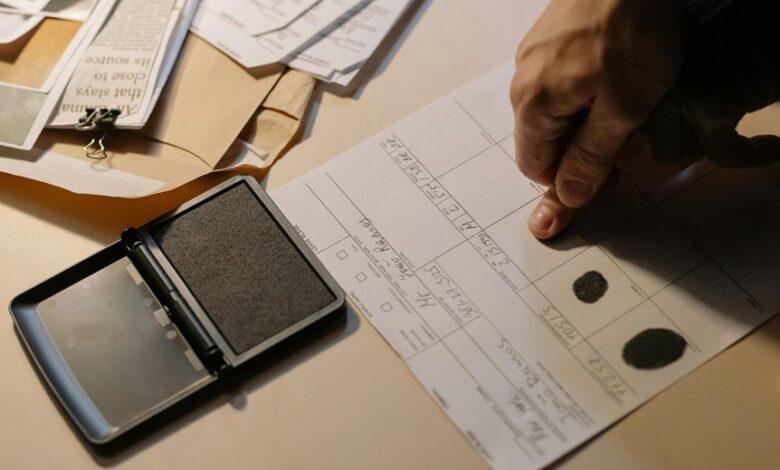
Digital identity verification refers to the process of confirming that a person’s claimed identity in a digital interaction corresponds to a real, verifiable individual or entity.
The practice anchors trust, enabling secure access and transactions while deterring fraud.
It emphasizes accountability and continuity across channels, with emphasis on privacy preserving methods, ensuring data minimization, user control, and transparent governance in identity verification frameworks.
How Verification Tech Is Used Across Platforms (Case Snapshots)
Across platforms, verification technologies are deployed to balance security, user experience, and compliance by tailoring methods to context; for instance, onboarding flows prioritize rapid identity checks with minimal data exposure, while high-stakes transactions employ multi-factor and biometric validation to deter fraud.
Case snapshots reveal verification pitfalls and identity spoofing risks, prompting platform-specific mitigations, policy alignment, and ongoing calibration of risk thresholds.
Key Challenges: Privacy, Security, and User Experience Trade-Offs
Navigating the triad of privacy, security, and user experience presents inherent trade-offs that shape identity verification strategies.
Organizations balance privacy trade offs against usable interfaces, risking friction or opt-in resistance.
Security considerations demand rigorous data protection, auditing, and multi-factor controls, yet may impede speed.
The optimal approach aligns policy, user autonomy, and technical safeguards to minimize risk while preserving accessibility and trust.
A Practical Framework to Evaluate Verification Solutions
A practical framework for evaluating verification solutions builds on the identified trade-offs between privacy, security, and user experience, translating high-level objectives into measurable criteria.
The framework emphasizes reproducible metrics, risk-based assessments, and modular testing.
It highlights identity theft mitigation and robust consent management, ensuring transparent data flows, auditable decisions, and user empowerment without compromising security or operational efficiency.
Conclusion
In this ledger of trust, identity is a gatekeeper and a shadowed corridor. The framework acts as a compass, steering through privacy’s fog and risk’s glare. Verification systems, like keystones, must balance light and weight—minimizing data while maximizing accountability. When decisions are auditable yet unobtrusive, and testing is modular, safeguards align with user dignity. Ultimately, governance becomes the hinge: secure enough to deter mischief, flexible enough to welcome legitimate onward journeys.




