Verify Call Record Entries – 2505814253, 5165493058, 18554399468, 8448859160, 3429588766, 8887077597, 7869271342, 4698385200, 9136778337, 97963939584
Verification of the listed call records requires a methodical approach to ensure accuracy and traceability. Each entry must be examined for timestamps, durations, participant IDs, routing paths, and outcomes, aligned across source systems. The process should emphasize tamper-evident logging and consistent formats while flagging anomalies for review. A concise, documented trail supports future reconciliations and privacy safeguards. Stakeholders will find the next steps essential to establish confidence, yet questions remain about how this verification will proceed.
What It Means to Verify Call Records
Verifying call records involves examining the details of telephone logs to confirm accuracy and integrity. The process centers on validating timestamps, durations, and connections, ensuring data remains consistent across sources. It requires disciplined methods and critical review to avoid misinterpretation. Calculation accuracy matters for conclusions, while privacy implications demand caution regarding disclosure and access, preserving user rights and data sovereignty.
Key Data Points to Audit in Each Entry
Auditing each call record entry requires enumerating the core data points that determine accuracy and traceability. Core fields include timestamp, caller ID, callee ID, duration, routing path, and outcome.
Verification checklist emphasizes verify records, audit points, and step by step reviews, highlighting common pitfalls.
Prevention methods focus on consistency, documentation, and anomaly alerting to maintain data integrity and trust.
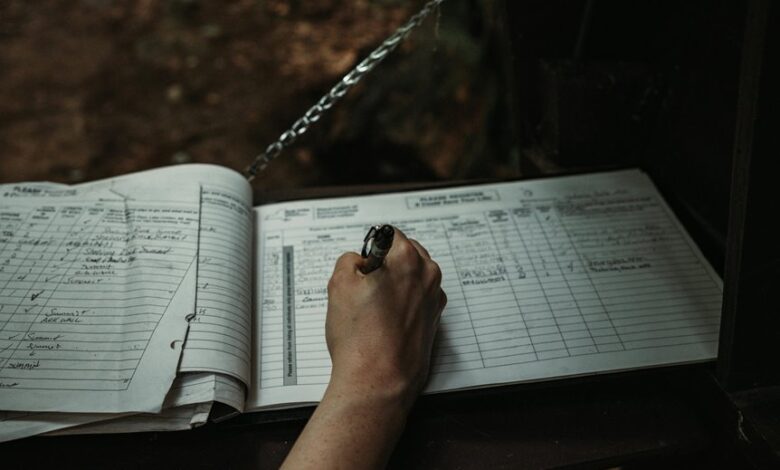
A Step-by-Step Verification Checklist
The checklist guides auditors through initial data capture, cross-referencing with source systems, and confirming timestamps, durations, and identifiers.
Call verification emphasizes consistency, while data integrity is preserved by logging changes, documenting exceptions, and maintaining tamper-evident records for accountability.
Common Pitfalls and How to Prevent Them
Common pitfalls in call record verification often arise from inconsistent data sources, incomplete metadata, and untracked edits. To mitigate risk, organizations should standardize data formats, capture complete metadata, and enforce immutable logs. Maintain an accessible audit trail and regular reconciliations. When issues emerge, verify records against authoritative sources, document corrections, and preserve evidence for future audits while preserving user autonomy.
Conclusion
Verification of call records hinges on meticulous cross-checking of timestamps, durations, parties, routing, and outcomes, with tamper-evident logging and auditable trails. This discipline ensures traceability and privacy, while enabling reliable future reconciliations. As the adage goes, “Trust, but verify.” By maintaining consistent data formats and promptly documenting corrections, organizations reduce anomalies and support compliant, transparent record-keeping. The approach remains concise, precise, and cautious, reinforcing integrity at every verification step.



