Audit Incoming Call Records – 2245096119, 887831407, 83512250804, 3372695110, 8332990168, 3509104130, 2536500841, 2673979949, 7052297336, 6313930636
Auditing the listed incoming call records requires a disciplined approach to verify provenance, timestamps, and transcript integrity across sources. A structured workflow should document deviations, enforce policy adherence, and ensure auditable change control. Independent validation and data lineage must tie retention, consent, quality, and security signals to each record. Privacy protections and robust voice authentication are essential, yet the discussion should remain restrained, outlining gaps and risks that prompt further examination rather than offering immediate resolution.
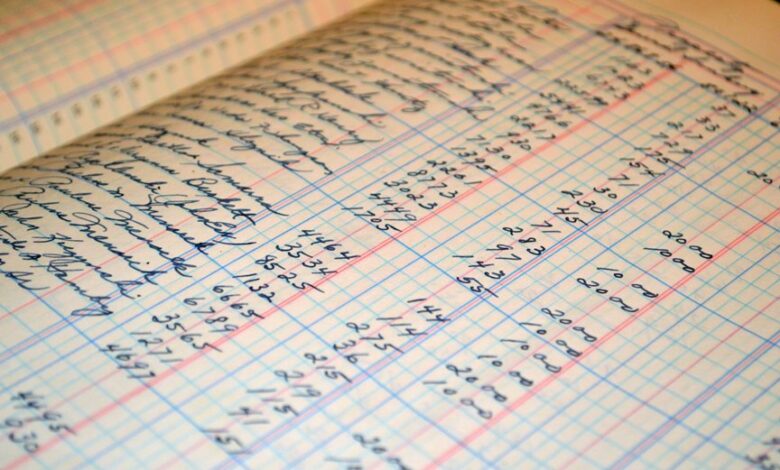
What Audit-ing Incoming Call Records Looks Like in Practice
Auditing incoming call records involves a structured examination of metadata and content to verify accuracy, completeness, and compliance. In practice, teams catalog call data provenance, verify timestamps, and assess data integrity across sources. Analysts compare transcripts with recordings, ensure policy adherence, and document deviations. When voice authentication is present, methods are evaluated for reliability, privacy, and auditable traceability.
How to Establish a Trustworthy Verification Workflow for Call Data
A trustworthy verification workflow for call data combines predefined criteria, disciplined data governance, and repeatable procedures to ensure accuracy and accountability. The framework emphasizes independent validation, auditable trails, and governance oversight. Verification workflow elements include source provenance, data lineage, and change control. Emphasis remains on preserving call data integrity, reducing risk, and enabling transparent, reproducible conclusions for stakeholders seeking freedom through reliable analysis.
Key Metrics and Anomaly Signals to Monitor in Logs
Key metrics and anomaly signals in logs provide the concrete evidence needed to assess call handling performance and security posture. The analysis emphasizes bias detection, data lineage, and performance metrics, supporting anomaly detection and regulatory alignment. Observations relate to user consent, call quality, data retention, and fraud signals, with encryption standards guiding data handling and ongoing data governance practices.
Privacy, Compliance, and Audit Trail Considerations for Telephony Data
The discussion emphasizes privacy governance, auditability, and lifecycle controls, ensuring lawful processing, access restrictions, and transparent retention.
Clear policies enable freedom while maintaining disciplined data handling, risk mitigation, and verifiable compliance across systems.
Conclusion
The audit of incoming call records demonstrates a disciplined, data-driven approach to verifying provenance, timestamps, and integrity across sources. By enforcing auditable trails, change control, and policy adherence, the process reduces ambiguity and supports reliable voice authentication while prioritizing privacy. The workflow functions as a finely tuned clockwork system—each component interlocks to detect deviations, document rationale, and preserve compliance. When signals align, confidence in data quality and governance is reinforced, enabling transparent, accountable outcomes.




