Account & Network Integrity Inspection – mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, Njgcrby
Account and Network Integrity Inspection, led by mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, and Njgcrby, frames a disciplined approach to authentication, authorization, and traceability. Robust monitoring and layered defenses are central, with clear governance, artifact inventories, and risk scenarios guiding action. The program emphasizes secure interconnections and rapid containment of integrity threats, while maintaining transparency and disciplined responses. A structured path forward exists, yet its implications and practical implications warrant careful examination as systems evolve.
What Account & Network Integrity Really Covers
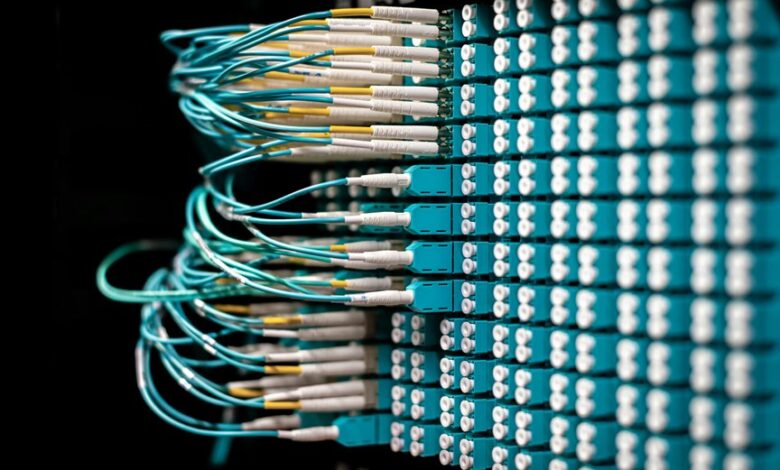
Account and Network Integrity encompasses the principles, controls, and processes that protect the authenticity of user identities, the consistency of system states, and the reliability of communications across a digital environment.
The scope emphasizes safeguarding authentication, authorization, and traceability, while maintaining data integrity and secure interconnections.
It foregrounds account integrity and network integrity as foundational pillars for trustworthy, freedom-driven digital operation.
How Proactive Monitoring Fortifies Your Environment
Proactive monitoring fortifies an environment by continuously surveying activity, configurations, and communications to detect deviations before they escalate into incidents. It relies on disciplined data collection, disciplined thresholds, and disciplined review cycles. Discovery flags guide anomaly baselines, enabling rapid identification of subtle outliers. This approach preserves autonomy while ensuring accountability, reducing risk, and sustaining resilient operations through rigorous, transparent governance and objective assessment.
Implementing Layered Defenses: Policies, Controls, and Response
The framework emphasizes data governance, rigorous risk assessment, and proactive access monitoring, ensuring early anomaly detection.
Decisions align with governance objectives, while layered controls enforce accountability, resilience, and rapid containment, enabling transparent, disciplined responses that preserve autonomy and support secure, freedom-centered operations.
Practical Steps to Start Your Own Integrity Inspection Program
Launching an integrity inspection program begins with a clear definition of scope, objectives, and governance—establishing what will be inspected, why it matters, and who holds accountability.
The approach proceeds with structured governance, risk assessment, and gap analysis, aligning with compliance frameworks.
Concrete steps include artifact inventory, risk scenarios mapping, measurement criteria, and iterative reviews to ensure continuous improvement and trusted integrity outcomes.
Conclusion
In the labyrinth of digital trust, integrity stands as the steadfast lighthouse. The program acts as a vigilant clock, each mechanism a precise gear turning toward transparency. Protocols, like unyielding sentinels, seal doors against misalignment; monitoring threads weave a net of early warning. Layered defenses form a fortress whose stones are evidence, audits, and accountability. When threats stir, rapid containment unfurls, a measured, disciplined catalyst—restoring balance and sustaining resilient, auditable operations under an unwavering, guiding light.




