Inspect Mixed Data Entries and Call Records – 111.90.1502, 1111.9050.204, 1164.68.127.15, 147.50.148.236, 1839.6370.1637, 192.168.1.18090, 512-410-7883, 720-902-8551, 787-332-8548, 787-434-8006
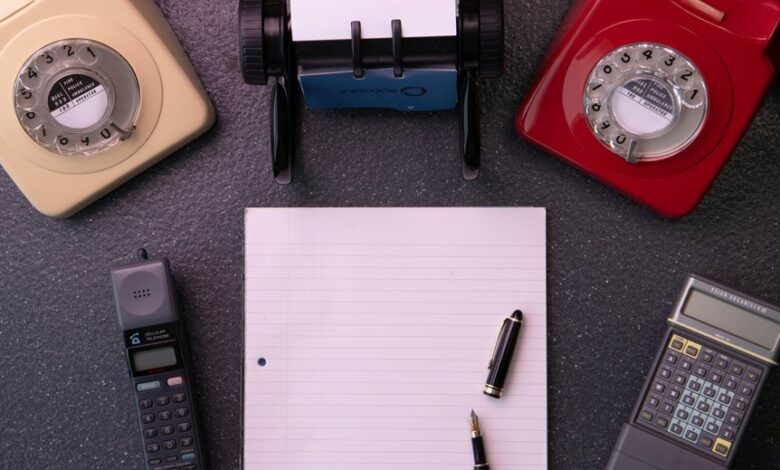
Mixed data entries blend IP-like strings and phone numbers into a single ledger, revealing cross-domain call activity patterns. The focus is on normalization and consistent formatting to enable clear links between timestamps, durations, origins, and outcomes. Methodical scrutiny highlights anomalies that cross data types and suggests reproducible workflows for auditing. The discussion points toward actionable validation and incident-response steps, but a critical question remains unresolved, inviting continued examination of how these hybrids affect traceability and response timing.
What Mixed Data Really Tells You About Call Activity
Mixed data entries provide a composite view of call activity by consolidating disparate data points—timestamps, durations, origins, and outcomes—into a single ledger.
The analysis identifies insight gaps and evaluates pattern cohesion across records, revealing how anomalies align with routine flows.
This methodical view clarifies reliability, informs auditing, and supports disciplined decision-making without overreliance on single metrics.
How to Normalize IP-Like Strings and Phone Numbers for Clarity
To standardize clarity across mixed data entries, the process of normalizing IP-like strings and phone numbers establishes uniform formats that reduce ambiguity in logs and call records.
The method analyzes segments, removes separators, and applies consistent spacing.
It enables reproducibility, facilitates searching, and supports parsing.
normalize strings, unify notations, then verify with deterministic rules and documented conventions.
Detecting Anomalies Across Data Types and Linkable Patterns
The method emphasizes insightful aggregation of signals from numeric, textual, and temporal sources, followed by structured anomaly taxonomy to categorize deviations.
Analysts uncover context-driven outliers, enabling precise interpretation and scalable detection without overfitting or unnecessary complexity.
Practical Validation, Correlation, and Incident Response Workflows
The approach favors conceptual auditing and disciplined evidence gathering, enabling a cross correlation workflow that formalizes hypothesis testing, artifact preservation, and repeatable containment, escalation, and remediation actions.
Conclusion
In a methodical, cross-checked fashion, the dataset converges where IP-like strings and phone numbers coalesce into a single activity stream. Coincidence becomes a visual thread: clustered digits echoing event timestamps, origin points, and call outcomes, suggesting standardized formats as a unifying lens. The apparent randomness recedes when normalized, enabling reproducible analyses, anomaly spotting, and rapid incident tracing, with each normalized entry acting as a beacon guiding investigators through a coherent, auditable trail.




